An investigation into Proton encrypted email.
Suddenly Silence
I'm a big user of email, preferring long chains to messaging apps for a lot of my friends and contacts. It's nice that it isn't tied to a single device or platform and since I own my domain, I can move it from service to service whenever I want and the sender doesn't have to learn some new address. However in the last two months I suddenly stopped getting emails from a percentage of my friends and even my mom.
What I was getting instead was PGP encrypted emails with blank bodies that looked like the following:
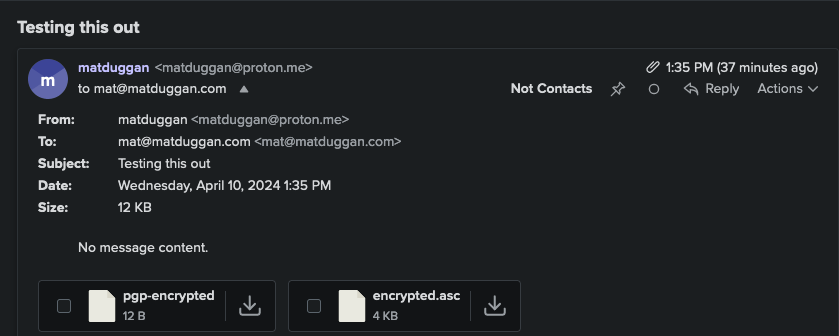
If I inspected the message, it was clearly an encrypted email which Fastmail doesn't support. They have a whole blog post on why they don't here: https://www.fastmail.com/blog/why-we-dont-offer-pgp/ but up to this point I haven't really cared one way or the other since nobody sends me encrypted emails.
Now I knew that Proton would send encrypted emails to other Proton email addresses, but obviously this isn't a Proton hosted email address which it would be able to tell pretty easily with DNS. Then it got even stranger when I tried my work email and got the same error.
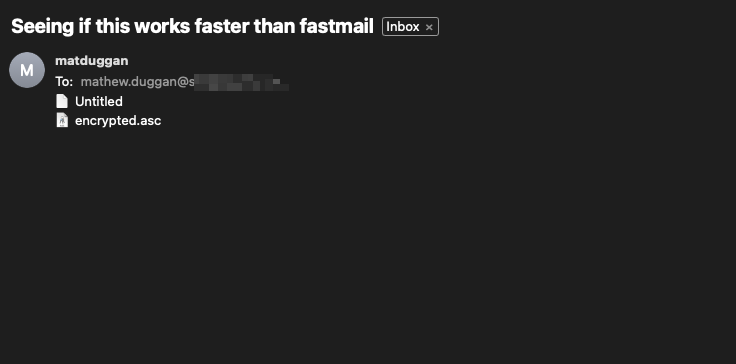
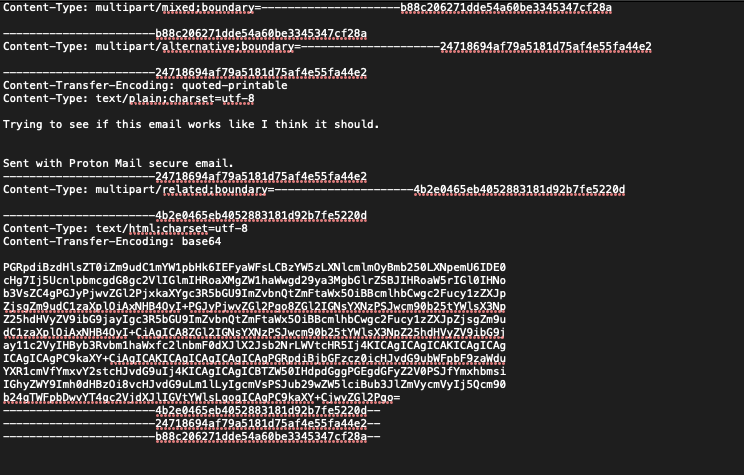
Checking the raw message and there it is, Proton has encrypted this email. Now this address is hosted on Google Workspaces, so at this point I'm just baffled. Can Proton email users not send emails to people on Google Workspaces email addresses? That can't possibly be right? My friends and mom using Proton would have noticed that their emails seem to always disappear into the ether for the majority of the people they email.
I open a ticket with Fastmail hoping they've seen this problem before, but no luck. Then I opened a ticket with Proton but didn't hear back as of the time of me writing this.
How Proton Seems To Work
So the reason why so many people I know are moving to Proton is they seem to be the only game in town that has cracked sending encrypted emails in the least annoying way possible. Their encryption uses asymmetric PGP key pairs with lookup for other users public keys happening on their key server. This in conjunction with their Key Transparency technology that compares lookup requests by the client with requests on the server-side allows for easy encrypted message exchanges with a high degree of safety, at least according to them.
There seems to be three classes of keys at Proton.
- User keys: encrypt account-specific stuff like contacts. Not shared.
- Address keys: for encrypting messages and data.
- Other keys: part of a key tree that leads back to the address key as the primary external key for people to use.
So that makes sense that Proton can lookup address keys for users on their system. But where are my keys coming from? So in their Proton Key Transparency whitepaper they have this little snippet on page 10:
For External Addresses, the server may return email encryption keys that it
found in the Web Key Directory (WKD) [6] (since email is hosted elsewhere).
The server may also return data encryption keys, used e.g. for Proton Drive.
The former should have an absence proof in KT, and the latter should have an
inclusion proof.
For Non-Proton Addresses, the server may also return keys that it found in the
WKD. This way clients can automatically encrypt emails to it. These keys won’t
be in ProtonKT, thus KT should return an absence proof.
What The Hell Is WKD?
WKD, or OpenPGP Web Key Directory is an IETF draft by Werner Koch. It describes a service where you can lookup OpenPGP keys by mail addresses using a service. It also allows the key owner and the mail provider to publish and revoke keys. The whole thing is very clever, an interesting way to get around the annoying parts of PGP encryption of email. You can read it here: https://www.ietf.org/archive/id/draft-koch-openpgp-webkey-service-16.txt
It outlines an enrollment process by which I would signal to a WKD service that I have a key that I want to enroll into the process. The only problem is I never did that, or at least certainly can't remember doing that. I'm certainly not hosting a page with any key verification stuff.
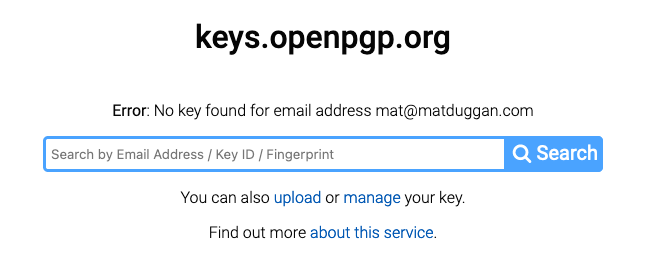
There seems to be a way to set a CNAME record to point towards keys.openpgp.org where I do have a key set, but that isn't set up on my domain.
nslookup openpgpkey.matduggan.com
Server: 2a01:4f8:c2c:123f::1
Address: 2a01:4f8:c2c:123f::1#53
Non-authoritative answer:
*** Can't find openpgpkey.matduggan.com: No answerSource here: https://keys.openpgp.org/about/usage
I can't seem to find why Proton thinks they can use this key BUT I can confirm this is the key they're encrypting the emails with.
What?
So it seems if your email address returns a key from keys.openpgp.org then Proton will encrypt the message with your public key from there, even though (as far as I can tell) I haven't opted into them using this service. I also can't seem to figure out a way to signal to them they shouldn't do it.
Alright so what happens if I just remove my key from keys.openpgp.org. The process is pretty simple, just go to: https://keys.openpgp.org/manage and follow the instructions in the email. It seems to work more or less instantly.
Alright looks like we figured it out!
Proton Seriously What The Hell?
I'm at a little bit of a loss here. I totally understand sending me encrypted emails if I've gone through the steps to set the CNAME that indicates that I want to do that, but it doesn't seem like that's how the service works. As far as I can tell, the act of uploading a OpenPGP-compatible key seems to trigger their service to send it as an end-to-end encrypted message.
I'll update this with whatever I hear back from Proton but in the meantime if you stumble across this post after getting blank emails from people for months, you'll at least be able to fix it.
Is there some flag I've accidentally set somewhere that tells Proton to send me encrypted emails? Let me know at: https://c.im/@matdevdug